Muy grave, he hecho muchos pagos por tarjeta de crédito y por PSE y me he fijado que en muchos de ellos las páginas no son HTTPS. ¿Quiere decir esto que en HTTP Telmex puede acceder a los datos que se están enviando al servidor?Imposible sin que Claro le obligue a instalar un certificado de raíz (root certificate) en su computador que les permita hacer el MitM (man-in-the-middle) de forma silenciosa. Si ese certificado raíz no está instalado en su computador e intentan interceptar HTTPS, absolutamente todas las conexiones HTTPS mostrarán error de certificado, y todo navegador Web reciente o le mostrará un aviso bien feo que lo disuadirá de continuar, o simplemente se rehusará a establecer la conexión dependiendo de la configuración del servidor.
Eso sí, el tráfico Web no HTTPS (HTTP) puede ser interceptado sin problema alguno.
[Claro - Internet Colombia] Foro oficial - (Dudas, inquietudes, sugerencias)
- Iniciador del tema Pikachu_Patapi
- WikiPost WikiPost
- Fecha de inicio
Estás utilizando un navegador obsoleto. Puede que este u otros sitios no se muestren correctamente.
Debes actualizarlo o utilizar un navegador alternativo.
Debes actualizarlo o utilizar un navegador alternativo.
- Estado
- El primer mensaje de este tema es un WikiPost y puede ser editado por cualquier persona. Tus ediciones serán públicas.
Muy grave, he hecho muchos pagos por tarjeta de crédito y por PSE y me he fijado que en muchos de ellos las páginas no son HTTPS. ¿Quiere decir esto que en HTTP Telmex puede acceder a los datos que se están enviando al servidor?
Sip.
Y no solo Telmex. Cualquer nodo por el que pase ese tráfico.
Pero me extraña lo de PSE, cualquier pasarela de pago está obligada a usar HTTPS, de lo contrario ninguna franquicia de tarjetas de crédito operaría con ellos. Debe estar confundido.
(Tenga en cuenta que es la pasarela de pagos la que debe ser HTTPS, el sitio no necesariamente)
En ese caso, tener instalado el HTTPS Everywhere sirve de algo?Eso sí, el tráfico Web no HTTPS (HTTP) puede ser interceptado sin problema alguno.
Ahora movistar con su fibra le va hacer competencia a claro y tigo estos son los nuevos planes son mas economicos que los que maneja claro
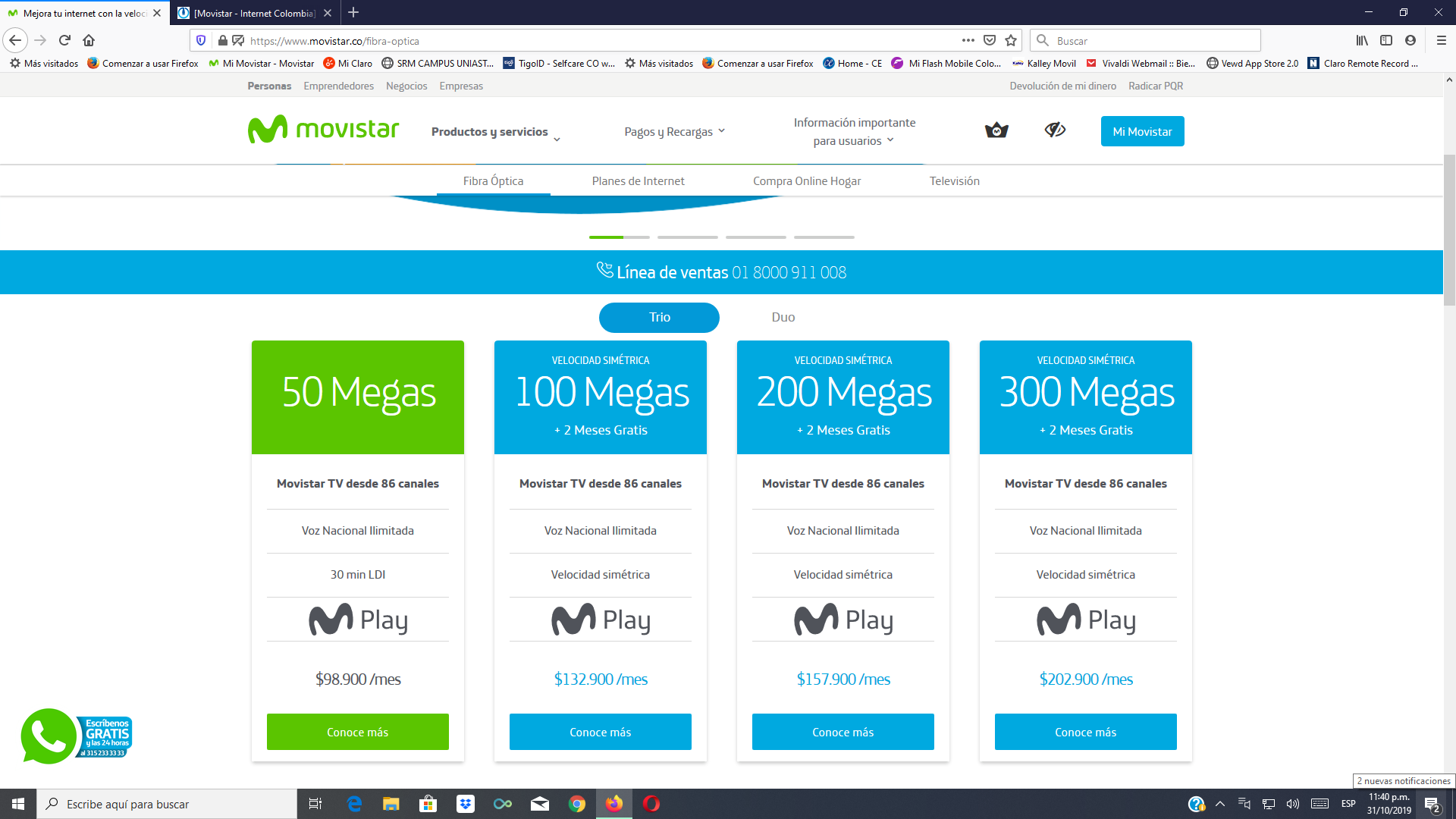
Ah pero no es posible, porque el compañero @-Jαv- dijo que Movistar fibra es muy caro en comparación con coaxial Comcel.

Escorpiom.
Escorpiom.
De pronto tus datos resultaron estar allá.Qué posibilidades hay que con ese filtrado puedan obtener información que viaje en HTTPS ?
Estoy un poco paranoico. Lo digo porque llevo años comprando y pagando por internet sin ningún problema y esta madrugada me apareció una compra no autorizada en mi tarjeta de crédito a AIRBNB. El operador de internet fijo que tengo en mi casa es CLARO.
Código:
https://actualidad.rt.com/actualidad/331990-robo-datos-tarjetas-bancos-vender-mercado-negroAcerca Fortiguard y SSL:
1. Full SSL inspection
When full SSL inspection is used, the FortiGate impersonates the recipient of the originating SSL session, then decrypts and inspects the content. The FortiGate then re-encrypts the content, creates a new SSL session between the FortiGate and the recipient by impersonating the sender, and sends the content to the sender.
When the FortiGate re-encrypts the content it uses a certificate stored on the FortiGate. The client must trust this certificate to avoid certificate errors. Whether or not this trust exists depends on the client, which can be the computer’s OS, a browser, or some other application, which will likely maintain it’s own certificate repository.
2. SSL certificate inspection
FortiGates also supports a second type of SSL inspection, called SSL certificate inspection. When certificate inspection is used, the FortiGate only inspects the header information of the packets.
Certificate inspection is used to verify the identity of web servers and can be used to make sure that HTTPS protocol isn't used as a workaround to access sites you have blocked using web filtering.
The only security feature that can be applied using SSL certificate inspection mode is web filtering. However, since only the packet is inspected, this method does not introduce certificate errors and can be a useful alternative to full SSL inspection when web filtering is used.
Con otras palabras, digamos que Comcel opta por método numero 2, en este caso no se le examina el paquete, sino el encabezado del paquete.
Con este metodo pueden asegurar que nadie salta los bloqueos de paginas web usando SSL.
No puedo decir con certeza cual de los metodos esta usando Comcel, numero 1 puede generar errores de certificado así que probablemente es método 2.
Lo anterior es información directamente de la pagina de FortiGate.
Escorpiom.
1. Full SSL inspection
When full SSL inspection is used, the FortiGate impersonates the recipient of the originating SSL session, then decrypts and inspects the content. The FortiGate then re-encrypts the content, creates a new SSL session between the FortiGate and the recipient by impersonating the sender, and sends the content to the sender.
When the FortiGate re-encrypts the content it uses a certificate stored on the FortiGate. The client must trust this certificate to avoid certificate errors. Whether or not this trust exists depends on the client, which can be the computer’s OS, a browser, or some other application, which will likely maintain it’s own certificate repository.
2. SSL certificate inspection
FortiGates also supports a second type of SSL inspection, called SSL certificate inspection. When certificate inspection is used, the FortiGate only inspects the header information of the packets.
Certificate inspection is used to verify the identity of web servers and can be used to make sure that HTTPS protocol isn't used as a workaround to access sites you have blocked using web filtering.
The only security feature that can be applied using SSL certificate inspection mode is web filtering. However, since only the packet is inspected, this method does not introduce certificate errors and can be a useful alternative to full SSL inspection when web filtering is used.
Con otras palabras, digamos que Comcel opta por método numero 2, en este caso no se le examina el paquete, sino el encabezado del paquete.
Con este metodo pueden asegurar que nadie salta los bloqueos de paginas web usando SSL.
No puedo decir con certeza cual de los metodos esta usando Comcel, numero 1 puede generar errores de certificado así que probablemente es método 2.
Lo anterior es información directamente de la pagina de FortiGate.
Escorpiom.
Yo no vine a pelear con uds ni soy empleado de Claro. Yo llame hace 3 días a Movistar y por mi barrio el. Precio que me dieron para 50 megas fue 150k ahora pago 104k y a excepción del coaxial tengo casi lo mismo, TV HD, 50 megas, pensé que eran 40 y no, teléfono. Pará mí 46mil pesos son diferencia.Ah pero no es posible, porque el compañero @-Jαv- dijo que Movistar fibra es muy caro en comparación con coaxial Comcel.

Escorpiom.
Por cierto, un Companero de la. Oficina se metió a Movistar y van 4 días que no le. Instalan nada, ayer fueron a su casa, pero los muy competentes solo le. Dejaron un deco Cúando eran 2, y ahora anda peleando por telefono a ver si le solucionan.
No digo que ni que Claro ni mucho menos Movistar tengan el mejor. Servicio al cliente, cada uno hace el negocio que le conviene.
No, hasta ahora solo servicios fijos.Estimados, disculpen la ignorancia, me podrían por favor indicar si este tema de filtrado y demás problemáticas descritas anteriormente afectan también la red móvil de Comcel (planes de datos), de antemano muchas gracias.
Acerca Fortiguard y SSL:
1. Full SSL inspection
When full SSL inspection is used, the FortiGate impersonates the recipient of the originating SSL session, then decrypts and inspects the content. The FortiGate then re-encrypts the content, creates a new SSL session between the FortiGate and the recipient by impersonating the sender, and sends the content to the sender.
When the FortiGate re-encrypts the content it uses a certificate stored on the FortiGate. The client must trust this certificate to avoid certificate errors. Whether or not this trust exists depends on the client, which can be the computer’s OS, a browser, or some other application, which will likely maintain it’s own certificate repository.
2. SSL certificate inspection
FortiGates also supports a second type of SSL inspection, called SSL certificate inspection. When certificate inspection is used, the FortiGate only inspects the header information of the packets.
Certificate inspection is used to verify the identity of web servers and can be used to make sure that HTTPS protocol isn't used as a workaround to access sites you have blocked using web filtering.
The only security feature that can be applied using SSL certificate inspection mode is web filtering. However, since only the packet is inspected, this method does not introduce certificate errors and can be a useful alternative to full SSL inspection when web filtering is used.
Con otras palabras, digamos que Comcel opta por método numero 2, en este caso no se le examina el paquete, sino el encabezado del paquete.
Con este metodo pueden asegurar que nadie salta los bloqueos de paginas web usando SSL.
No puedo decir con certeza cual de los metodos esta usando Comcel, numero 1 puede generar errores de certificado así que probablemente es método 2.
Lo anterior es información directamente de la pagina de FortiGate.
Escorpiom.
El método 2 simplemente quiere decir que filtra el acceso a sitios analizando el certificado enviado por el sitio y si corresponde a un sitio en una lista negra, bloquea la conexión. Pero es eso, simplemente bloquear el acceso a sitios por HTTPS, este método no puede inspeccionar el contenido del tráfico como en el método 1 puesto que no descifra el tráfico como sí lo hace el método 1.
El método 1 además dice:
When the FortiGate re-encrypts the content it uses a certificate stored on the FortiGate. The client must trust this certificate to avoid certificate errors. Whether or not this trust exists depends on the client, which can be the computer’s OS, a browser, or some other application, which will likely maintain it’s own certificate repository.
Con el método 1 se puede inspeccionar el contenido del tráfico HTTPS, pero siempre va a tirar error de certificado a no ser de que el usuario seleccione la opción de confiar en el certificado (lo cual es una opción muy difícil de acceder en los navegadores más recientes, a diferencia de hace algunos años).
Estimados, disculpen la ignorancia, me podrían por favor indicar si este tema de filtrado y demás problemáticas descritas anteriormente afectan también la red móvil de Comcel (planes de datos), de antemano muchas gracias.
Hasta ahora solamente servicios fijos pero seguramente será algo que terminarán implementando en el internet móvil también.
Hoy fueron a la casa a revisar el tema de las filtradas, ni Bing, ni Tumblr, ni taringa. Cuando yo le dije que solo abría por vpn, el man ni siquiera sabía que era vpn lo que me hace pensar que los contratistas pobres ellos pero están mal capacitados. A la final se fue sin solucionar m
Y me dice que en 24 hrs solucionan , de entrada ya le había dicho que la cosa no era de tecnico
Y me dice que en 24 hrs solucionan , de entrada ya le había dicho que la cosa no era de tecnico
A ellos los capacitan en solo ponchar cable y en calibrar valores de HFC, que estén en un rango y ya. Yo hablé con un técnico y me dijo que muchos son solamente bachilleres sin ningún tipo de formación adicional, los capacitan en un guión y yaHoy fueron a la casa a revisar el tema de las filtradas, ni Bing, ni Tumblr, ni taringa. Cuando yo le dije que solo abría por vpn, el man ni siquiera sabía que era vpn lo que me hace pensar que los contratistas pobres ellos pero están mal capacitados. A la final se fue sin solucionar m
Y me dice que en 24 hrs solucionan , de entrada ya le había dicho que la cosa no era de tecnico
^^
Si, es correcto. Creo que el tema principal es de dinero, jóvenes sin mucha formación es una fuente de mano de obra barata.
Los que realmente saben están en el noc o son ingenieros externos.
Eso de visitas técnicas de Comcel no es muy eficiente. Si mandan una cuadrilla y la falla es de redes externas o noc, realmente no hay mucho por hacer.
Algunos usuarios reciben multiples visitas y la falla persiste.
Es un desperdicio de recursos.
Escriba bien.
Escorpiom.
Si, es correcto. Creo que el tema principal es de dinero, jóvenes sin mucha formación es una fuente de mano de obra barata.
Los que realmente saben están en el noc o son ingenieros externos.
Eso de visitas técnicas de Comcel no es muy eficiente. Si mandan una cuadrilla y la falla es de redes externas o noc, realmente no hay mucho por hacer.
Algunos usuarios reciben multiples visitas y la falla persiste.
Es un desperdicio de recursos.
Por cierto, un Companero de la. Oficina se metió a Movistar y van 4 días que no le. Instalan nada, ayer fueron a su casa, pero los muy competentes solo le. Dejaron un deco Cúando eran 2, y ahora anda peleando por telefono a ver si le solucionan.
Escriba bien.
Escorpiom.
Yo tuve que pasar por la misma situación de reportar fallas en la red del proveedor, en una instalación de fibra en un centro comercial de Bogotá. No se podía acceder a los servicios de la ip pública desde la misma red donde esta operaba porque haciendo un traceroute no pasaba de esas ips 10.xx.xx.xx tipicas de las nat. Finalmente remedieron alla luego de 10 llamadas pero querían mandarme un técnico con cobro adicional.Lo mismo acá, me llamaron a pedir soportes.
Me enojé muchísimo porque se están haciendo los bobos. Les pregunté explicitamente si estaban filtrando trafico y me dijeron que no, que no tenían idea que eso pasaba.
Les envié nuevamente un correo con toda la info relevante.
Como es posible que el usuario tiene que detectar fallas en la red del proveedor y enviar pruebas que estas fallas existen?
Es el mundo al revés?
Los de Comcel son unas momias que solo sirven para mentir, tramposos estafadores.
Hasta ahora sin solución alguna.
Escorpiom.
Lo ideal es que sean técnicos laborales en mantenimiento de PC , de redes o de sistemas . que a pesar de que son carreras que toman solo 1 añp o año y medio uno aprende mucho al ser mas practico que teorico, la verdad si me dejo aterrado que no supiera que era una vpn , solo fue a hacer ping . si son bachilleres solamente estamos llevados . lo que si se es que los supervisores de ellos si deben al menos tener una tecnología en el area de sistemasA ellos los capacitan en solo ponchar cable y en calibrar valores de HFC, que estén en un rango y ya. Yo hablé con un técnico y me dijo que muchos son solamente bachilleres sin ningún tipo de formación adicional, los capacitan en un guión y ya
lo que si se es que los supervisores de ellos si deben al menos tener una tecnología en el area de sistemas
Según me dijo un tecnico, los supervisores son tecnicos que son ascendidos, por el tiempo que llevan, y su buen comportamiento, y no por el estudio que tengan.
al que fue hoy fue al que le pregunte y me dijo que tenia que ser tecnologo pero tal vez si es tecnico con mucha exp tambien aplique , no se la verdad . Para ser consultor o asesor en un CAV oficial ,si debe ser tecnologo y se gana 1.6 Millones , pues yo el año pasado me iba a presentar pero me dio perezaSegún me dijo un tecnico, los supervisores son tecnicos que son ascendidos, por el tiempo que llevan, y su buen comportamiento, y no por el estudio que tengan.
Los últimos temas
-
¿El Regreso de BLACKPINK Podría Ser una Realidad en 2026?
- Iniciado por Aldair Goyzuetas
- Respuestas: 0
-
-
-
-